Intro

A couple years I obtained CISM so it might be useful to compare the certifications. While CISM was useful, it is not specific to any particular framework and most standards are simply mentioned for context or trivia. You can read about it here: My CISM journey
Every now and then I face a problem at my work, that I need to understand better to contribute in a productive way.
Enter the NIS2
When NIS2 came along, I had to assess the applicability and required controls. The requirements for risk management, incident handling, information security policies, supply chain management…etc, with a bit of EU specifics. ENISA provides a mapping to ISO 27001 and other frameworks and thus began my analysis of our internal ISMS.
What is ISO 27001?
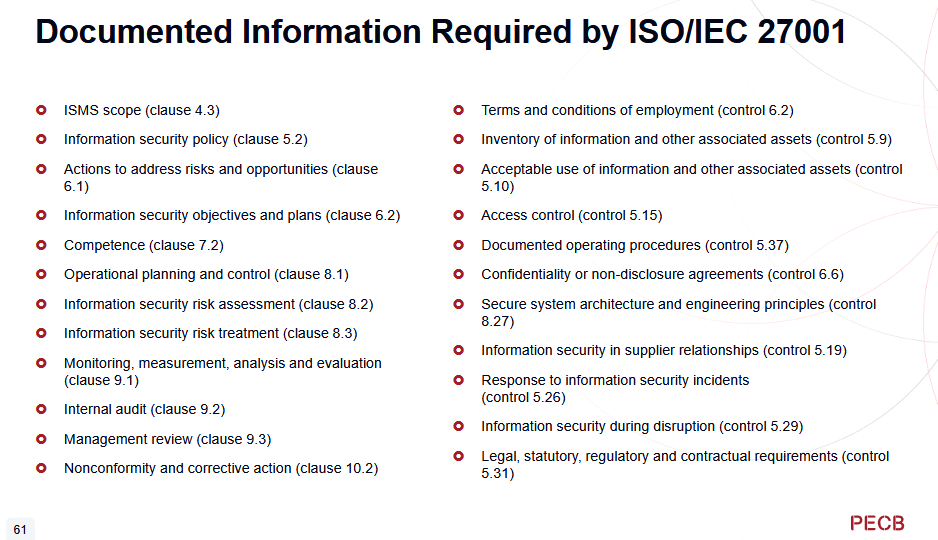
ISO 27001:2022 is information security management system(ISMS) used in many organizations worldwide, that provides structured guidelines to manage cybersecurity risks.
Annex A provides a list of security controls a company has to evaluate and/or implement:
-
Organizational controls (37 measures)
-
People controls (8 measures)
-
Physical controls (14 actions)
-
Technological controls (34 measures)
Every company I worked for was either certified, or at least aligned with ISO 27001 requirements. Despite that, I did not know enough about the inner workings of the framework and did not care to learn about it - it concerned mostly “boring” corporate IT, and I preferred to have more specific technical skills rather than managing security awareness programs or phishing simulations.
-
Every suit under the sun claims to have ISO 27001 knowledge
-
every company claims to be certified, is in process of recertifying, is doing a yearly audit,
-
is dealing with self-inflicted change management processes and software
-
is filling their risk registers with information that is performative or irrelevant, or can’t deal with the backlog of risks
-
ISO 27001 does not guarantee the company will not get breached
-
implementing and tracking the 93 Annex A controls sounds like a bother!
So you can see how I was not so thrilled before, because my focus is R&D, product security and Cyber Resilience Act.
NIS2 and Industrial Security
NIS2 concerns not only IT systems, but organization as a whole, especially in strategically important areas such as manufacturing. So OT risk management also has to be considered.
Not to say that companies don’t have know-how to manage it, rather it does not follow the same processes as IT. And why should they - OT risks are different, concern physical machines so it’s not just Confidentiality/Integrity/Availability but also Health, Safety, Environment. OT also has hardware that does not follow the same lifecycle or technological curve as IT systems.
Still, when defining actions to be taken for NIS2 and establishing organization context, most of it could be found in company ISO 27001 security policy and ISMS. There may be a world where we can afford running two concurrent security programs in IT and OT, but because Industry 4.0 and “IT OT convergence” is an actual thing, a more unified approach is needed. So I need complete understanding of both IEC 62443, ISO 27001 and NIS2 to determine the approach going forward.
PECB ISO 27001 Lead Implementer training
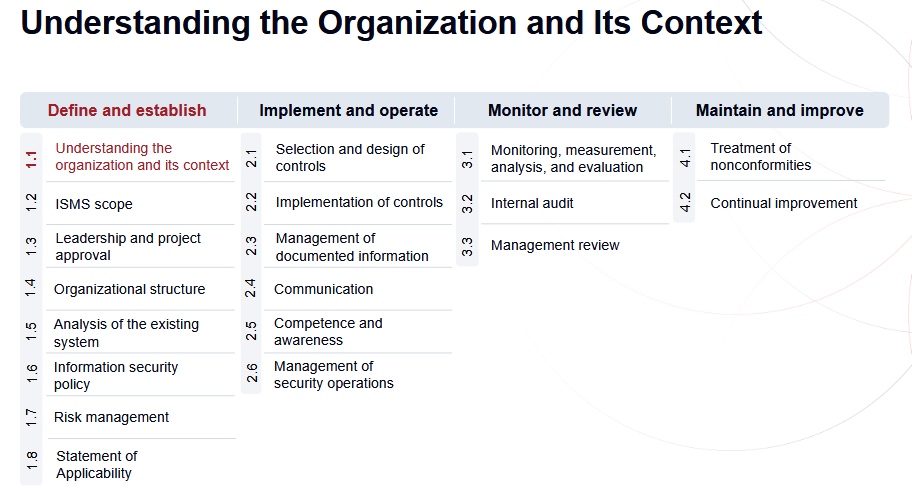
As the name suggests, the course deals with implementation of the ISMS. It is relevant when implementing new system or working on an existing one.
Where auditor is focused on evaluating ISMS compliance, implementer may start ISMS projects, do risk assessments, implement controls or work on security improvements inside the organization long-term.
Depending on where you buy it from, the price will be around 1100 - 1600$/€ for the online course. In Switzerland, the official PECB partner is SGS academy.
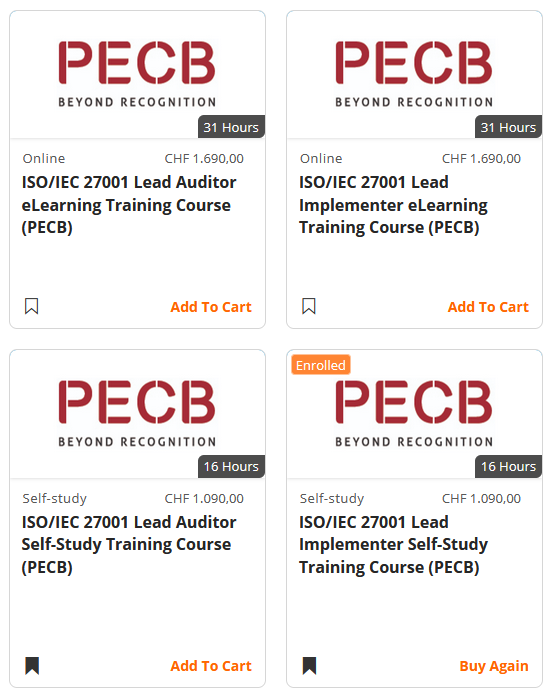
This is a popular course and you may find other partner training providers, in-person training and coaching, for extra price of course. I prefer self-paced learning, and implied budget limits for training lead me to cheaper options. You may find trainings outside PECB at different prices but it is well-recognized and worth the price.
Reading the standard alone will not prepare you for implementation or audit processes, so the training also brushes upon potential approaches depending on organization maturity level, budget and culture. If all you look for is a badge and a certificate JPEG, you might gamble on 100$ course, and if you really understand the standard as a result, good for you!
Course materials
Course materials consists of:
-
4 slide decks with notes, each for one day (realistically it takes more time to absorb the material)
-
Case studies
-
Exercises
-
Quizzes
Case study is a long example of a fictional company security context, architecture and summary of risk assessment, later used in exercises to test readers understanding.
Exercises let you practice your risk assessment, policy and control skills. This is useful to step back and read material in order to understand how to use ISO 27001 to meet organizational goals.
Quizzes are either stand-alone checkpoints after each chapter, or scenario based multiple-choice-questions. Both type of questions appear in the exam so they are useful training. Quizzes and exercises have correction keys so you can also know the correct answer and expectations.
I did not use any external trainings or quizzes but I have extensive cybersecurity experience and a live ISMS at my employer to allow me to contextualize the standard vs our own policies, risk assessments and audit notes.
I really really appreciate the course materials being relatively short, dense and concise. There is no repetiveness or slop, just well structured course that covers all the bases. ( have you taken Azure courses? those are probably the worst).
I went through the materials in 2 weeks, studying during working hours on the side of my job. Once finished, I registered for the exam at earliest available slot.
Exam
The exam is open-book multiple-choice-question test, 80 questions , 3 hours. Check to make sure you follow the policy on what is allowed, but at the time I was allowed to have a paper standard, and slides from the course inside examination app. Sometimes I would check the slides to make sure I understood the control or some clause correctly, but overall the test was smooth. The ambiguity is relatively low. I scored 83% so even then my interpretation differs from that of auditors or examinator on the best approach.
After confirming my professional references and professional experience, I now possess the “Lead Implementer” title. The latter requires 5 years of experience and 300 ISMS project hours. Since ISMS and security work is so large in scope, it is hard NOT to have enough relevant experience if you work in infosec.
The takeaways
Learning the standard made me realize that often times organizations or auditors misunderstand the standard because they did not learn it properly. Too often the risk management process is ill-informed and organizational bureaucracy takes hold, especially when dealing with nonconformities. Auditors may get hung up on old ways of documenting Statements of Applicability, or certain controls, not knowing the flexibility of the framework.
Flexibility of ISO 27001 allows to pick controls from other frameworks and make your own, not limited to ISO 27001 Annex A. This means we could have controls from IEC 62443 and scope it to industrial assets we deem critical.
On the other hand, enlarging ISMS scope introduces complexity, delays compliance and increases workload for audits. Parts of OT risk management processess may have to reside outside ISO 27001 scope, but it can still be integrated into company ISMS. There is also less need to redefine company policies because the same organizational context, risk measurement methods, incident response processess and reporting chains can be used. The documentation approach, selection and documentation of controls, non-conformities and performing reviews is also something that can be borrowed from ISO 27001.
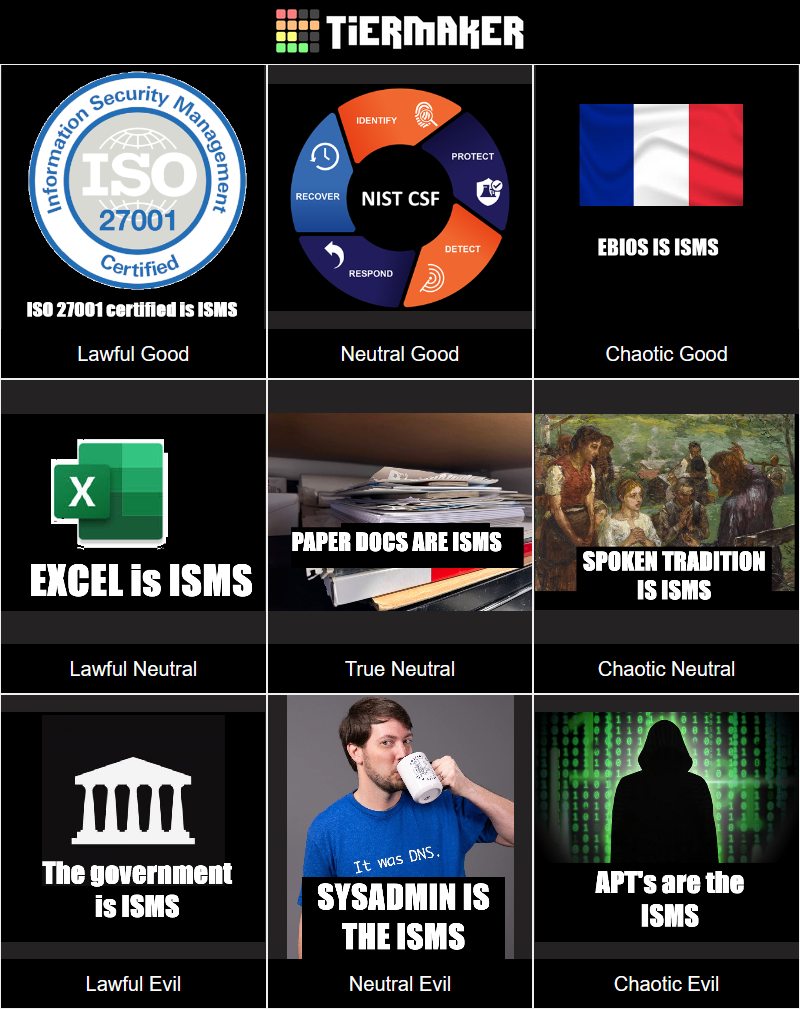
In the end, ISMS can be any system that accomplishes company security goals and can take on many forms. ISO 27001 is a good and structured framework to reach them, but not the only one.
Risk assess all the things!
A method I was using extensively already was the risk assessment. Risk assessment is used as a starting point for any effort - not just when testing a product or website, but also when evaluating applicable laws, actions and controls.
The training even proposes to risk assess your trainings.
-
What is the objective?
-
What is gained, what gets delayed?
-
What are the outputs of the training?
Here’s how my raw notes looked like
our obj - NIS 2 - via ISO 27001 inclusion
need - iso 27001 expertise
output - certification, practical standard knowledge
cost - minimal (1.2k) . time investment - 2 weeks ~
risks and opportunities - slowdown of backlog (negligible),
network incentives still on track , policies are being produced,
reviewed and documented. slowdown of German learning
long term benefit - alignment of internal company A and B ISMS
CISM comparison
CISM - more focused on the business side of infosec mission. For example, according to CISM cyber is just another risk and the benefit of security program must be higher than the cost.
ISO 27001 on the other hand, stipulates that it is the goal of the system to meet applicable laws, so the system , chosen controls and documentation must reflect that. Failing that, the system might as well be considered non-compliant.
CISM also goes into detail about forensics, legal aspects, corporate governance concerns.
ISO 27001 knowledge is not unique skill in itself, but when combined with other frameworks it is immensely useful for cybersecurity professionals. Had my life turned out differently, I could have started as ISMS intern in Paris and perhaps learned the standard much earlier. It is also likely that I would have lost important technical capability and love for the craft. Now that I am more experienced, I can appreciate a good standard, compliance structure and long-term thinking.
On the other side of the training I came out with good understanding of the risk management lifecycle, ways to document nonconformities and correctly addressing them.
Further reading
This is just my interpretation from my experience with IEC 62443, industrial security frameworks and ISO 27001.
Attempts to bridge OT and IT security programs are taking place at the standard level for example:
ISO/IEC TS 27103:2026 Technical spec provides guidance on using ISO and IEC standards in a cybersecurity framework, including IEC 62443 (allegedly). While I still have not read the standard, it is only natural that ISMS must concern itself to industrial risks when applicable.
Learning old fashion way
Since it is the year 2026, everything has to be AI. But in order to use the AI you still have to understand the subject matter behind it.
I am sure someone is working on self-implementing agentic ISO 27001 ISMS, capable of gathering it’s own inventories, assessing the risks, assigning reponsibilities (to other agents), writing policies and reporting to the CISO.
But before we are obsolete, there still needs to be a human in the loop.
” Claude, certify ISO 27001 and make no mistakes! “
Even if it was successful, I wouldn’t know anything about the process or the system in question, hindering me as a professional. Now that I learned it, I can use AI tools for specific tasks if I wanted to, and be able to cross-check it with the standard, or original materials, without relying on GPT results which are sourced from vendor specific websites trying to sell you things (incentives matter!).
Remaining certified
As with other ISO/IEC 17024 accredited certifying institutions, one must pay annual maintenance fees and prove continuous learning. PECB allows you to submit work project hours in the field, and not just vaporware “training” with dubious participation rewards. In “Lead Implementer” case, 90 hours over 3 year period seems easy to file (compare to ISACA’s awful CPE system I wrote about before..), in addition of the usual conferences and trainings you can do. Just this week, we were creating new risk assessment templates and onboarding internal users in a seminar. If you keep track of your project work , it should be a breeze to keep the certification.